Container Scanning (ULTIMATE)
Introduced in GitLab Ultimate 10.4.
Overview
If you are using GitLab CI/CD, you can check your Docker images (or more precisely the containers) for known vulnerabilities by using Clair and clair-scanner, two open source tools for Vulnerability Static Analysis for containers.
You can take advantage of Container Scanning by either including the CI job in
your existing .gitlab-ci.yml file or by implicitly using
Auto Container Scanning
that is provided by Auto DevOps.
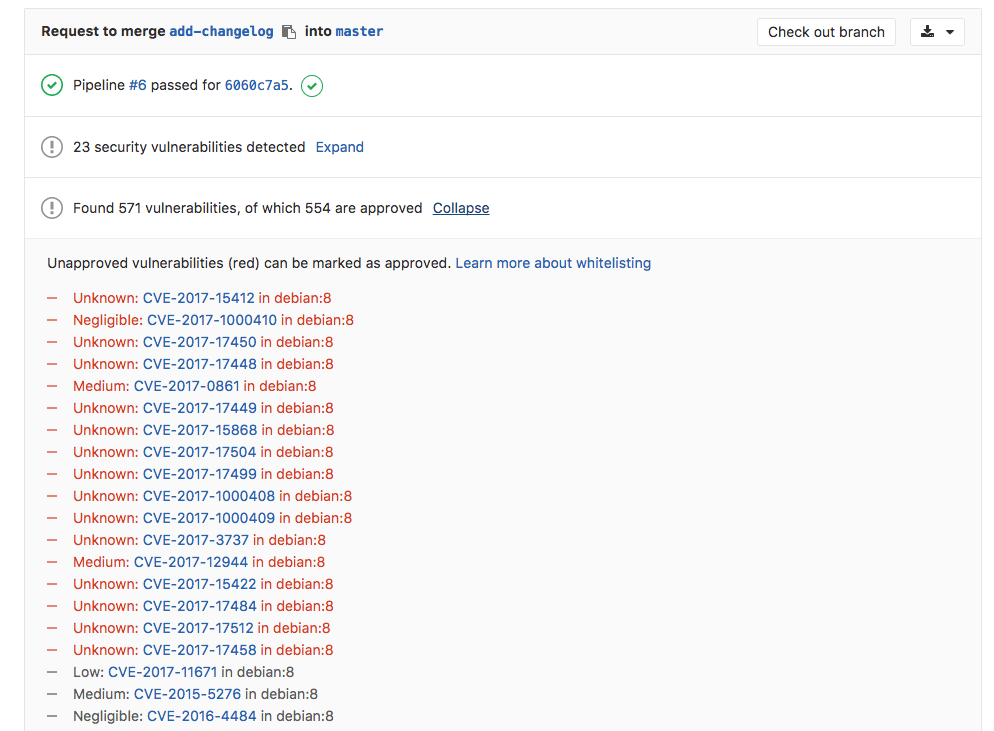
GitLab checks the Container Scanning report, compares the found vulnerabilities between the source and target branches, and shows the information right on the merge request.
Use cases
If you distribute your application with Docker, then there's a great chance that your image is based on other Docker images that may in turn contain some known vulnerabilities that could be exploited.
Having an extra job in your pipeline that checks for those vulnerabilities, and the fact that they are displayed inside a merge request, makes it very easy to perform audits for your Docker-based apps.
Requirements
To enable Container Scanning in your pipeline, you need:
-
A GitLab Runner with the
dockerorkubernetesexecutor running in privileged mode. If you're using the shared Runners on GitLab.com, this is enabled by default. -
Docker
18.09.03or higher installed on the machine where the Runners are running. If you're using the shared Runners on GitLab.com, this is already the case. -
To build and push your Docker image to your project's Container Registry. The name of the Docker image should match the following scheme:
$CI_REGISTRY_IMAGE/$CI_COMMIT_REF_SLUG:$CI_COMMIT_SHAThe variables above can be found in the predefined environment variables document.
Configuration
For GitLab 11.9 and later, to enable Container Scanning, you must
include the
Container-Scanning.gitlab-ci.yml template
that's provided as a part of your GitLab installation.
For GitLab versions earlier than 11.9, you can copy and use the job as defined
in that template.
Add the following to your .gitlab-ci.yml file:
include:
template: Container-Scanning.gitlab-ci.ymlThe included template will:
- Create a
container_scanningjob in your CI/CD pipeline. - Pull the already built Docker image from your project's Container Registry (see requirements) and scan it for possible vulnerabilities.
The results will be saved as a Container Scanning report artifact that you can later download and analyze. Due to implementation limitations, we always take the latest Container Scanning artifact available. Behind the scenes, the GitLab Container Scanning analyzer is used and runs the scans.
If you want to whitelist some specific vulnerabilities, you can do so by defining
them in a YAML file named clair-whitelist.yml. Read more in the
Clair documentation.
Security Dashboard
The Security Dashboard is a good place to get an overview of all the security vulnerabilities in your groups and projects. Read more about the Security Dashboard.
Interacting with the vulnerabilities
Once a vulnerability is found, you can interact with it. Read more on how to interact with the vulnerabilities.
Vulnerabilities database update
For more information about the vulnerabilities database update, check the maintenance table.
Troubleshooting
docker: Error response from daemon: failed to copy xattrs
When the GitLab Runner uses the Docker executor and NFS is used
(e.g., /var/lib/docker is on an NFS mount), Container Scanning might fail with
an error like the following:
docker: Error response from daemon: failed to copy xattrs: failed to set xattr "security.selinux" on /path/to/file: operation not supported.This is a result of a bug in Docker which is now fixed.
To prevent the error, ensure the Docker version that the Runner is using is
18.09.03 or higher. For more information, see
issue #10241.