SCIM provisioning using SAML SSO for Groups (SILVER ONLY)
Introduced in GitLab.com Silver 11.10.
System for Cross-domain Identity Management (SCIM), is an open standard that enables the automation of user provisioning. When SCIM is provisioned for a GitLab group, membership of that group is synchronized between GitLab and the identity provider.
GitLab's SCIM API implements part of the RFC7644 protocol.
Currently, the following actions are available:
- CREATE
- UPDATE
- DELETE (deprovisioning)
The following identity providers are supported:
- Azure
Requirements
-
Group SSO needs to be configured.
-
The
scim_groupfeature flag must be enabled:Run the following commands in a Rails console:
# Omnibus GitLab gitlab-rails console # Installation from source cd /home/git/gitlab sudo -u git -H bin/rails console RAILS_ENV=productionTo enable SCIM for a group named
group_name:group = Group.find_by_full_path('group_name') Feature.enable(:group_scim, group)
GitLab configuration
Once Single sign-on has been configured, we can:
- Navigate to the group and click Settings > SAML SSO.
- Click on the Generate a SCIM token button.
- Save the token and URL so they can be used in the next step.
Identity Provider configuration
Azure
The SAML application that was created during Single sign-on setup now needs to be set up for SCIM.
-
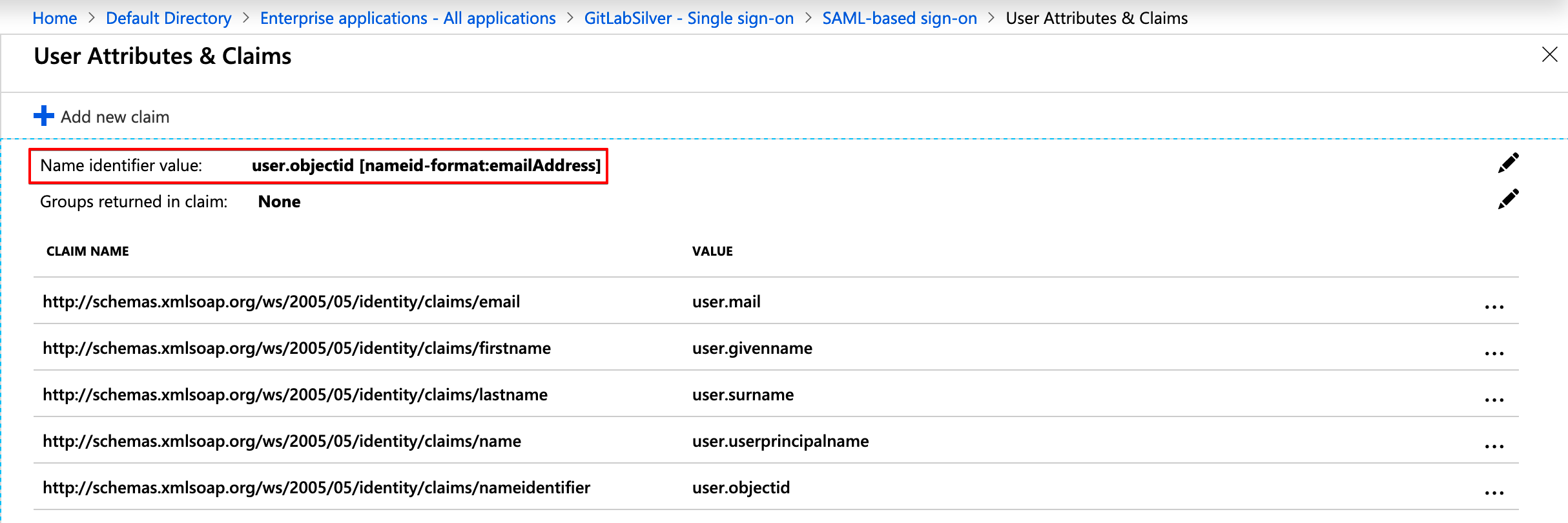
Check the configuration for your GitLab SAML app and ensure that Name identifier value (NameID) points to
user.objectidor another unique identifier. This will match theextern_uidused on GitLab. -
Set up automatic provisioning and administrative credentials by following the Provisioning users and groups to applications that support SCIM section in Azure's SCIM setup documentation.
During this configuration, note the following:
- The
Tenant URLandsecret tokenare the ones retrieved in the previous step. - Should there be any problems with the availability of GitLab or similar errors, the notification email set will get those.
- It is recommended to set a notification email and check the Send an email notification when a failure occurs checkbox.
- For mappings, we will only leave
Synchronize Azure Active Directory Users to AppNameenabled.
You can then test the connection by clicking on Test Connection. If the connection is successful, be sure to save your configuration before moving on. See below for troubleshooting.
Configure attribute mapping
-
Click on
Synchronize Azure Active Directory Users to AppName, to configure the attribute mapping. -
Click Delete next to the
mailmapping. -
Map
userPrincipalNametoemails[type eq "work"].valueand change it's Matching precedence to2. -
Map
mailNicknametouserName. -
Create a new mapping by clicking Add New Mapping then set Source attribute to
objectId, Target attribute toid, Match objects using this attribute toYes, and Matching precedence to1. -
Create a new mapping by clicking Add New Mapping then set Source attribute to
objectId, and Target attribute toexternalId. -
Click the
userPrincipalNamemapping and change Match objects using this attribute toNo.Save your changes and you should have the following configuration:
NOTE: Note: If you used a unique identifier other than
objectId, be sure to map it instead to bothidandexternalId. -
Below the mapping list click on Show advanced options > Edit attribute list for AppName.
-
Leave the
idas the primary and only required field.NOTE: Note:
usernameshould neither be primary nor required as we don't support that field on GitLab SCIM yet. -
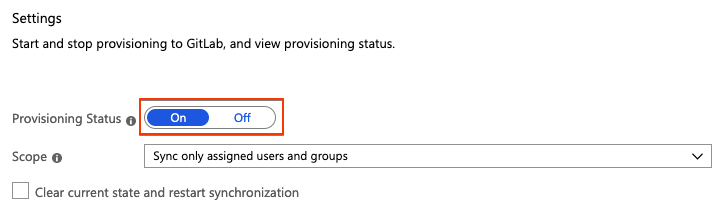
Save all the screens and, in the Provisioning step, set the
Provisioning StatustoOn.NOTE: Note: You can control what is actually synced by selecting the
Scope. For example,Sync only assigned users and groupswill only sync the users assigned to the application (Users and groups), otherwise, it will sync the whole Active Directory.
Once enabled, the synchronization details and any errors will appear on the bottom of the Provisioning screen, together with a link to the audit logs.
Troubleshooting
Testing Azure connection: invalid credentials
When testing the connection, you may encounter an error: You appear to have entered invalid credentials. Please confirm you are using the correct information for an administrative account. If Tenant URL and secret token are correct, check whether your group path contains characters that may be considered invalid JSON primitives (such as .). Removing such characters from the group path typically resolves the error.
Azure: (Field) can't be blank sync error
When checking the Audit Logs for the Provisioning, you can sometimes see the
error Namespace can't be blank, Name can't be blank, and User can't be blank.
This is likely caused because not all required fields (such as first name and last name) are present for all users being mapped.
As a workaround, try an alternate mapping:
- Follow the Azure mapping instructions from above.
- Delete the
name.formattedtarget attribute entry. - Change the
displayNamesource attribute to havename.formattedtarget attribute.